Configuration Profile settings
Real-time Protection
This setting allows you to control the behaviour of real-time protection.
Exclusions
If you find that a particular item is repeatedly mistakenly detected as a threat by the Windows Defender scanner, you can add it to an exclusion.
You can then use Exclusions on the Configuration Profiles tab in the ribbon bar to decide which item to add to the exclusion. You can choose to exclude files, file extensions, entire directories and/or processes. This step also allows you to use wildcards when defining the exclusion list:
| Placeholder | Use |
| * (asterisk) | For filenames and file extensions, the asterisk replaces any number of characters and applies only to files in the last directory specified in the exclusion. For folder exclusions, the asterisk replaces a single folder. |
| ? (questition mark) | For file names and file extensions, the question mark replaces a single character and applies only to files in the last directory defined in the exclusion. For folder exclusions, the question mark replaces a single character in a folder name. After matching the number of folders with wildcards and named folders, any subfolders are also included. |
| Environment variables | The defined variable is filled as a path when the exclusion is evaluated. |
You can also add any number of exclusions to a configuration profile and attach an exclusion to any number of configuration profiles.
Actions for threats
This is where you define the actions to be taken when a threat is detected on the Client. For the four different threat levels (Severe, High, Medium, Low) you can choose between the maintenance actions Quarantine, Remove and Ignore.
Cloud Based Protection
This protection feature causes files unknown to Defender to be pre-scanned by Microsoft. So if an unknown threat, such as a new virus, appears on the client, Defender will upload the possible threat to Microsoft for further investigation, leaving the decision on whether to proceed to Microsoft.
SmartScreen
This feature helps protect you from malware and phishing websites when you use applications and data, and when you use Microsoft Edge. SmartScreen automatically alerts you when a threat is detected, blocks access to a webpage or file, or blocks an application from running with a warning message.
Controlled folder access
Here you can define untrusted and trusted directories. Add entire directories that you consider untrustworthy. However, if individual applications are safe, you can explicitly classify them as trusted. These will then be excluded from the monitored directory. The latter can be set to Block, Monitor mode, Block changes to disks only and Monitor disks only.
UI
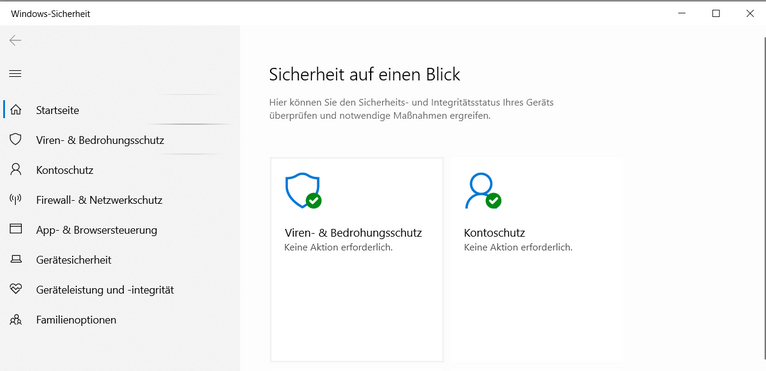
Here you can specify elements of the graphical user interface on the client, such as preventing or allowing General and Defender pop-ups or other notifications. You can also control which individual Windows security modules are displayed in the GUI.
Configuration Profile settings
Headless UI mode
When this setting is enabled, all graphical elements on the client related to Defender are disabled. This means, for example, that virus and threat protection notifications are not displayed.
Scan settings
Allows you to configure various scanning options.
General Scan settings
Here you can configure various scan settings.
Scan settings for Data
In addition to scanning archive files, such as ZIP folders, you can also set the maximum scan size for files and attachments that are scanned by default during a download.
Quick Scan settings
Set the interval and time for the daily quick scan.
Scheduled System scan
A scheduled System Scan allows you to run a full Client virus scan at a time of your choosing.
By default, the Full System Scan feature is not enabled. If you enable the scan, the settings you have previously specified will take effect. The settings include the time of the scan and the level of CPU usage.
Update settings
This configuration allows you to define general update settings, as well as the exact update sources and time intervals for updates.
General Update settings
Here you can configure various update settings, as well as the timing of out-of-date security information.
Update source
These settings allow you to specify file shares and a custom order of update sources.
Update scheduling
Set the days of the week, times and intervals for scheduled security information updates.
Attack Surface Reduction
Attack surface reduction (ASR) rules allow you to target specific software behaviour to reduce the potential attack surface for threats.
These rules prevent risky software behaviour, such as launching executables and scripts that attempt to download and execute files, performing suspicious application behaviour, or executing suspicious files and scripts in general. You can enable 15 different rules to either monitor or immediately block the process.
| Rules for reducing the attack surface | Description |
| Block executable content from email client and web email | Prevents .exe, .dll or SCR file types and PowerShell .ps, Visual Basic .vbs or JavaScript.js script files from running from emails that are opened while using Microsoft Outlook or Outlook.com. |
| Prevent all Office applications from creating child processes |
Prevents Office (Word, Excel, PowerPoint, OneNote and Access) from creating child processes. This prevents malware from hijacking Office applications to run VBA macros. |
| Prevent Office applications from creating executable content | Prevents malicious code from being written to the hard drive by preventing Office applications (including Word, Excel and PowerPoint) from creating potentially malicious executable content. |
| Prevent Office applications from inserting code into child processes | Prevents Office applications from being exploited externally by adding malicious code through code injection. This applies to Word, Excel and PowerPoint. |
| Block potentially hidden scripts from running | Detects and blocks suspicious properties in an obfuscated script. Script obfuscation is used to hide intellectual property or reduce script load times. |
| Block Win32 API calls to Office macros | Prevents VBA macros from calling Win32 APIs. Office VBA allows Win32 API calls. Malware can abuse this feature, for example by calling Win32 APIs to execute malicious shellcode without writing anything directly to the hard disk. |
| Block executable files from running unless they meet a distribution, age, or trusted list criterion | This rule blocks the launching of .exe, .dll or SCR file types unless they meet the prevalence or age criteria, or are included in a trusted list or exclusion list. To allow specific processes of these file types, use the Exclusions ASR rule. |
| Block Windows credential stealing for local security authorities | Prevents credential theft by locking down the Local Security Authority Subsystem Service (LSASS). LSASS authenticates users logging on to a Windows computer. Microsoft Defender Credential Guard normally attempts to extract credentials from LSASS during this process. However, some organisations may not be able to enable Credential Guard on all computers. These compatibility issues can occur with custom smart card drivers or other programs that load into the Local Security Authority (LSA). |
| Block process creation via PSExec and WMI commands | Blocks the execution of processes created via PsExec and WMI. Both PsExec and WMI can execute code remotely, so there is a risk that malware could exploit this functionality for command and control purposes or to spread an infection across the corporate network. |
| Block untrusted and unsigned processes running from USB | This rule allows administrators to prevent unsigned or untrusted executable files from being run from USB removable media, including SD cards. Blocked file types include executable files (such as .exe, .dll, or SCR). |
| Prevent Office communications application from creating child processes | This rule prevents Outlook from creating child processes while allowing legitimate Outlook functions to run. This rule protects against social engineering attacks and prevents code from being used to exploit Outlook vulnerabilities. It also protects against Outlook rule and form exploits that attackers can use if a user's credentials are compromised. |
| Prevent Adobe Reader from creating child processes | This rule prevents attacks by preventing Adobe Reader from creating processes. By preventing the creation of child processes by Adobe Reader, it prevents the propagation of malware that attempts to use it as an attack vector. |
| Use advanced ransomware protection | This rule provides additional protection against ransomware. It uses both client and cloud heuristics to determine whether a file resembles ransomware. |
| Prevent JavaScript and VBScript from launching downloaded executables | This rule prevents scripts from launching potentially malicious downloaded content. Malware written in JavaScript or VBScript often acts as a downloader to fetch and launch other malware from the web. Although not common, business applications sometimes use scripts to download and launch installers. |
| Block persistence via WMI event subscription | This rule prevents malware from using WMI to persist on a device. Fileless threats use various tactics to stay hidden, avoid being seen in the file system, and maintain regular execution control. Some threats may abuse the WMI repository and event model to stay hidden. |
ASR rule exclusions
If you have an ASR rule enabled but want to allow certain files and directories that it would normally block, you can create exclusions for ASR rules. Add folders or files via the appropriate exclusion field to allow them despite the rule being enabled.
Linking scheduled scans to Configuration Profiles
You can link scheduled scans to configuration profiles. You create different scan jobs by selecting Scheduled Scans from the Configuration Profiles tab in the ribbon bar.
In the dialogue box, specify the interval and the configuration profiles to which the scan will be linked. You will see all the links from the scheduled scans and the selected configuration profile in the workspace under Linked Scheduled Scans.
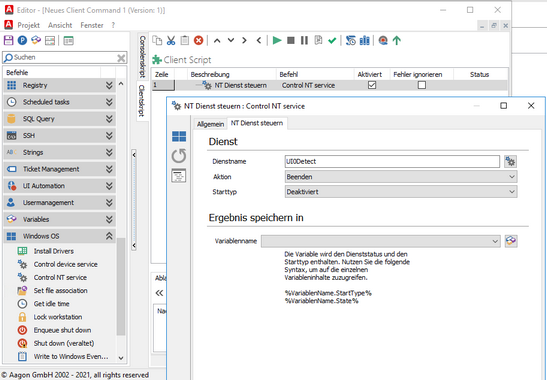
Client Command NT Control Services